Quality content, on demand
Get a vetted writer to deliver quality content, fast. From blog posts to ad copy (and everything in between), we’ve got you covered.
Money-back guarantee for your first 4,000 words.Free revisions and rewrites.
Submit a content request in under 5 mins. We handle the rest.
Get Started
“Draft takes care of the whole copywriting process end to end. They've been great at helping us get our larger pipeline of content out quickly.”
Submit your content request
Use our brief builder or upload your own brief on our platform.
Utilize our Zapier integration to submit your requests directly from tools such as Asana or Monday.
A writer matched in 24 hrs. and working on your content
We'll match you with the best writer in under 24 hrs. and have them start working on your brief.
Collaborate with your matched writer via our in-app messaging tool.
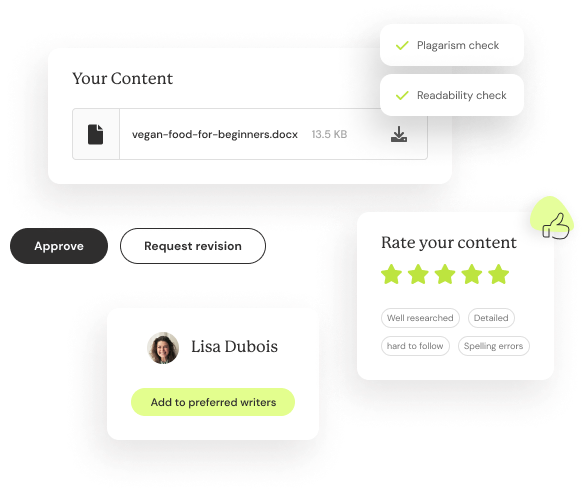
Publish ready content delivered. Free revisions and rewrites.
By the stated deadline get your publish-ready content piece back.
Need tweaks? We offer free revisions and rewrites until you're happy. All self-served via our app.
AI-powered workflows
We've built tools to help you with idea generation, brief creation, collaboration, and more. All 100% free.
An extended writing team
Uber-style ratings will help our algorithms assemble a fractional writing team that consistently works for you and knows your brand and editorial guidelines.
Tech-enabled collaboration
We've built chat features and specific editorial workflows to enable quick, easy adjustments to your content pieces.
Idea generator and brief builder
Use our free AI tools to generate content ideas, create a brief or generate article outlines.

“Draft has been instrumental in helping us scale our content while maintaining high quality that both users and search engines love. We've beaten all projections thanks to the fantastic team at Draft."
Vetted writers covering
a broad range of topic and types
We boast a 4.8/5 content quality rating on our platform. We've created content for over 16,000 customers spanning SMBs to Enterprise.
A typical writer on our platform has a 4.8 star customer rating and a rewrite rate of <1%. We rigorously vet writers and only accept the best.
We have over 1,000 writers spanning the US/Canada, UK and AU/NZ to handle various dialects and regional nuances.
Our writers come with experience in a variety of topics and content types. Not sure if we handle your niche? Contact us on live-chat.
Every content piece goes through plagiarism detection using Copyscape before it's delivered to you.
We pass content through our AI content detection tool to ensure it's 100% human generated.

“With Draft, we found a risk-free solution for high-quality content. If there is ever any issue with the writing, the team is quick to provide revisions, & even find a new writer if it's really not a good fit.”
Simple
pay-as-you-use pricing
No contracts. No commitments.
If we don't crush it, you get your money back. We’ll refund your purchase (up to the first 4000 words).
A blog post of 1,000 words will cost you USD 100. Back to you in 5 days

“Draft is the best writing service I’ve ever used. We’ve published in publications like the Wall Street Journal and Inc Magazine.”
What's included?
- Research
- Royalty-free images
- Unlimited revisions
- Live-chat support
Looking for managed services or high volume discounts? Contact us.
FAQ
Your most common questions about Draft, answered.
It takes 30 seconds to sign up for a Draft account and get access to your content creation dashboard. Create a content brief and get matched with the best writer to take it on. You can message your writers directly through the platform and track their progress. If you'd like any revisions made, you can do so free of charge!
The writers at Draft can take on a variety of content formats, essentially anything written. Primarily we handle blog posts, social posts, web page copy, and marketing emails. If there's something specific you're looking for, email us at support@draft.co or shoot us a message on chat and we'll see if we can help you with your specific content needs!
With our flexible pay-as-you-go pricing, you can request as many content pieces as you'd like to be worked on in parallel. A content piece that's 1,000 words in length will be returned back in five days. Revisions and rewrites are not charged extra.
We do preliminary research on all content using publicly available information and include sources for any facts or statistics we quote. Please specify your requirements for citations if applicable.
Creating perfect content the first time can be tough, so we offer free revisions on any content you receive in case you'd like some tweaks. Our goal is to get you content that you're happy with and delivers value to your readers!
Sign up for our newsletter
Join our monthly email with marketing insights and feature updates.





